Ping Identity as external authentication method for Microsoft Entra ID (Azure AD)
Description
Estimated time to complete: 45 minutes.
In this use case, you configure Advanced Identity Cloud as an external authentication method for Microsoft Entra ID (formerly Azure AD) using OIDC. This lets a user from Microsoft Entra ID use Advanced Identity Cloud as a second-factor authentication solution.
Goals
After completing this use case, you’ll know how to do the following:
-
Configure a custom OIDC application for SSO
-
Configure Microsoft Entra ID to use an external authentication method (EAM)
-
Configure a custom journey for multi-factor authentication (MFA) purposes
Before you begin
Before you start work on this use case, ensure you have these prerequisites:
-
A basic understanding of:
-
SSO and federation
-
OIDC
-
Microsoft Entra ID
-
JavaScript
-
-
Access to your Advanced Identity Cloud development environment as a tenant administrator.
-
A test Microsoft Entra ID environment with at least a P1 license. Learn more in Microsoft Entra licensing options.
-
An administrator with the Privileged Role Administrator or Global Administrator role in Microsoft Entra ID.
-
A test user in Advanced Identity Cloud to serve as the application owner for the custom OIDC (Microsoft Entra ID) application.
-
A test end user. The use case matches a user from Microsoft Entra ID to a test user in Advanced Identity Cloud. Specifically the user must have the same username and password.
Tasks
| This use case requires the use of third-party services. Use your environment specific details where necessary. |
Task 1: Create a new OIDC web application in Advanced Identity Cloud
-
In the Advanced Identity Cloud admin console, go to Applications > Custom Application > OIDC - OpenId Connect > Web.
-
Create an application with the following configuration:
Field Value Sign-in URLs
https://login.microsoftonline.com/common/federation/externalauthproviderGrant Types
ImplicitScopes
openidAccess: Response Types
id_tokenAccess: Claims
profileAuthentication: Token Endpoint Authentication Method
None
Task 2: Set up Microsoft Entra ID as the service provider
In this task, you prepare Microsoft Entra ID to serve as a service provider (SP) and use Advanced Identity Cloud as an external authentication method.
|
Learn more about setting up Microsoft Entra ID to integrate with an external method in the Microsoft Entra product documentation. |
Register a new app
-
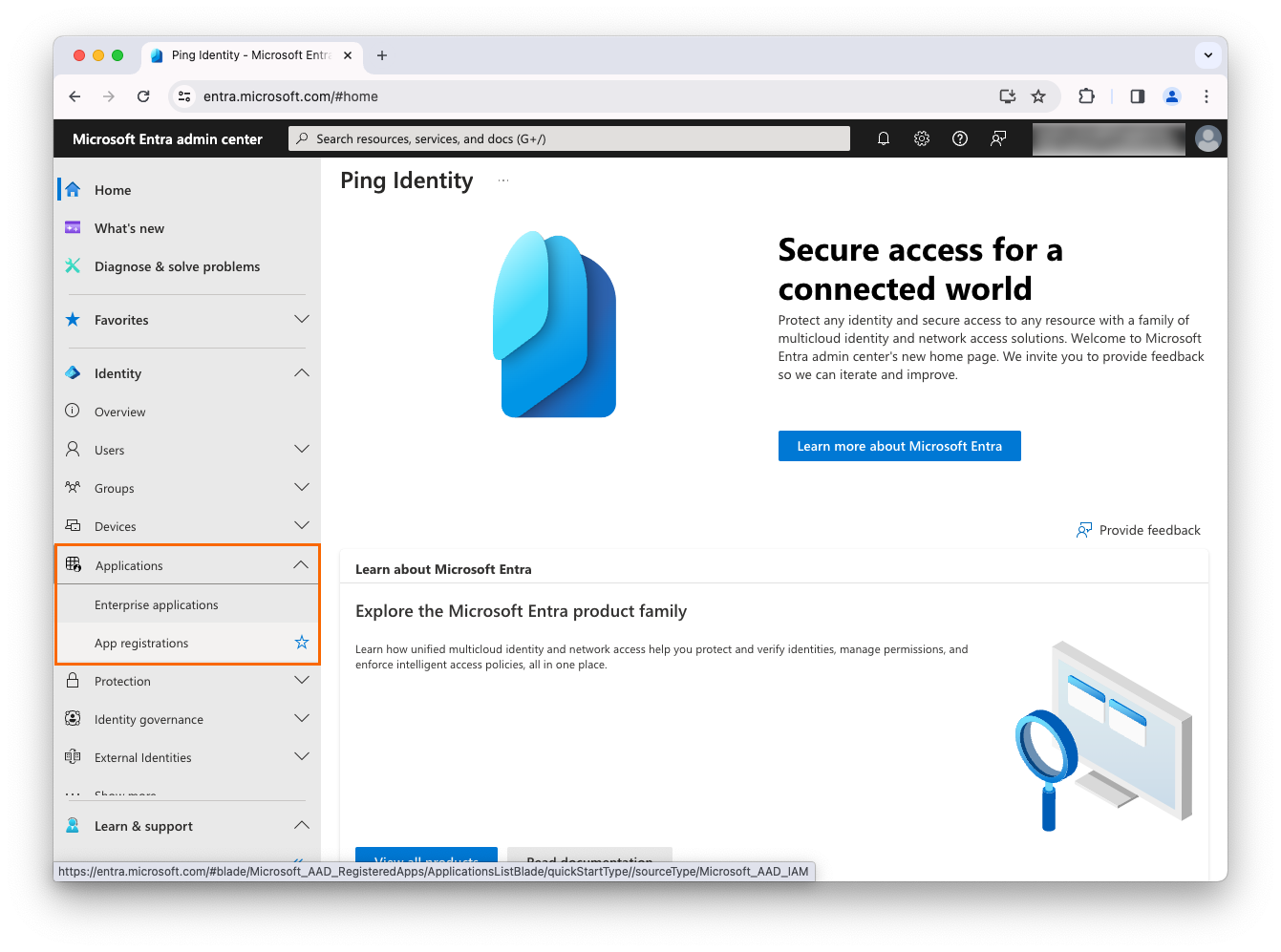
In a browser, navigate to the Microsoft Entra admin center.
-
Click Applications and then click App registrations.
-
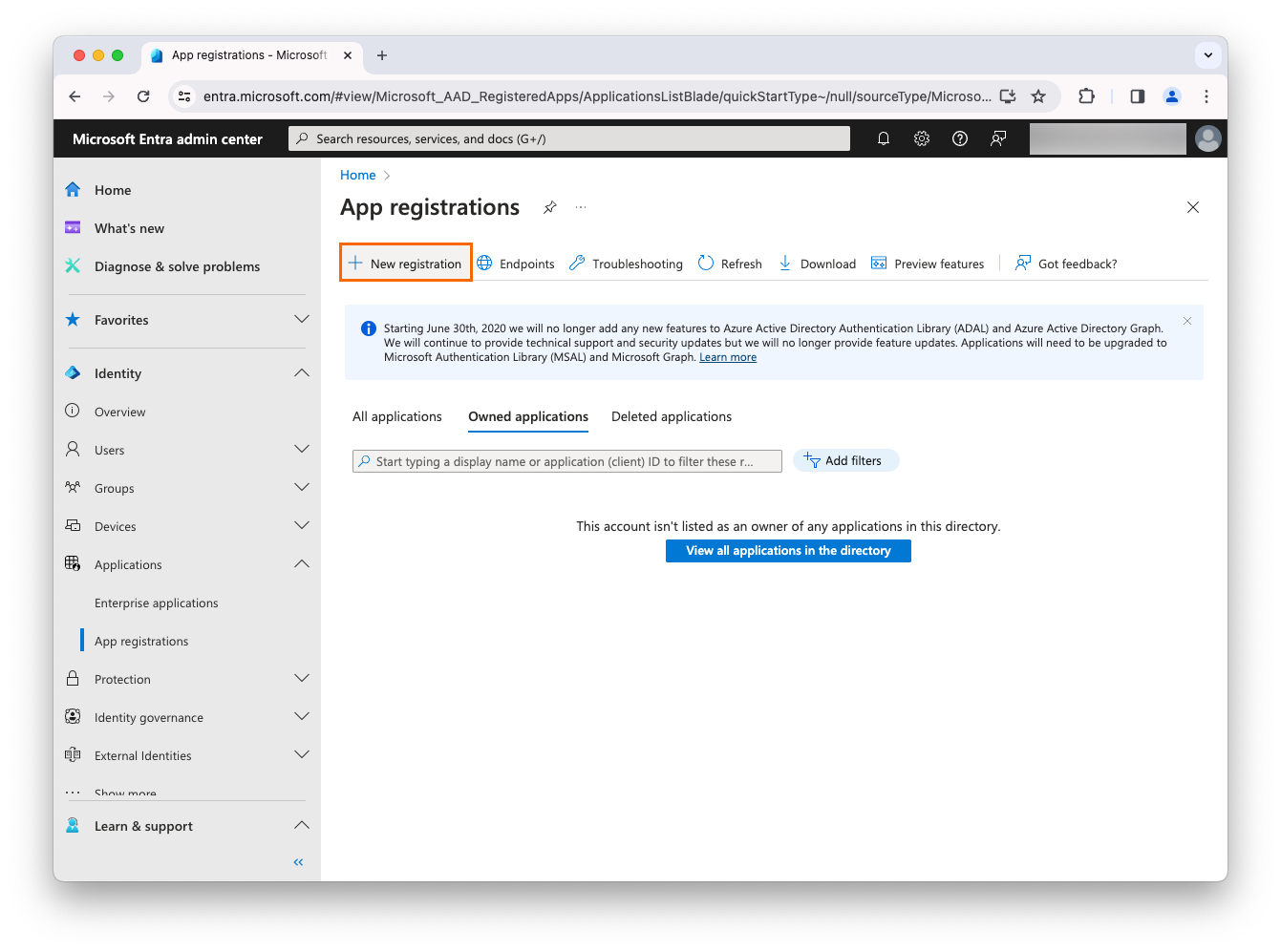
In the top toolbar, click New registration.
-
Complete the following fields:
Field Value Name
The app name (for example,
AIC-EAM-DOC)Supported account types
Select Accounts in this organizational directory only (... - Single tenant)
Redirect URI
Your Advanced Identity Cloud authorization endpoint. For example,
https://<tenant-env-fqdn>/am/oauth2/alpha/authorize.Select a platform
Web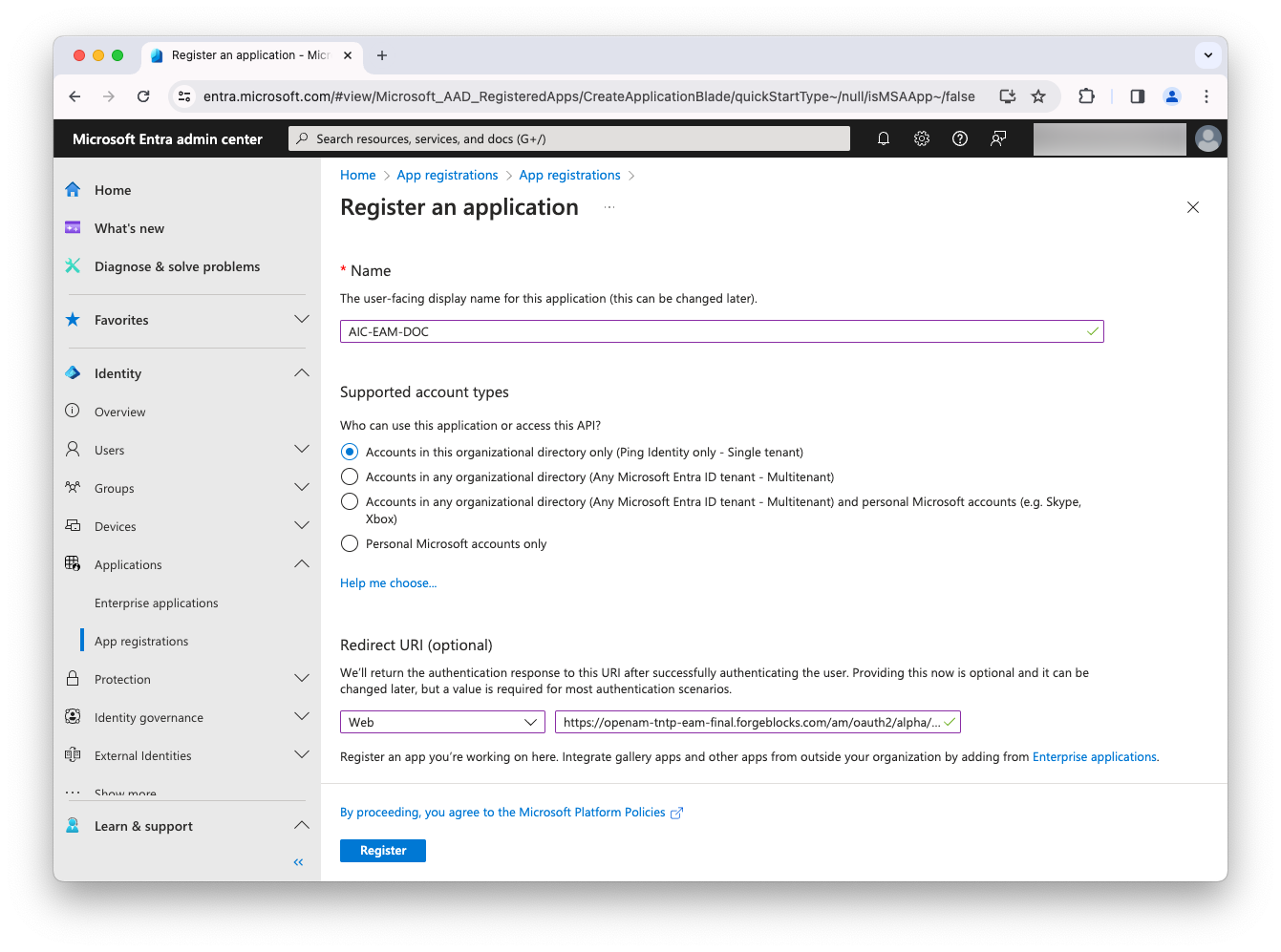
-
Click Register to create the application.
-
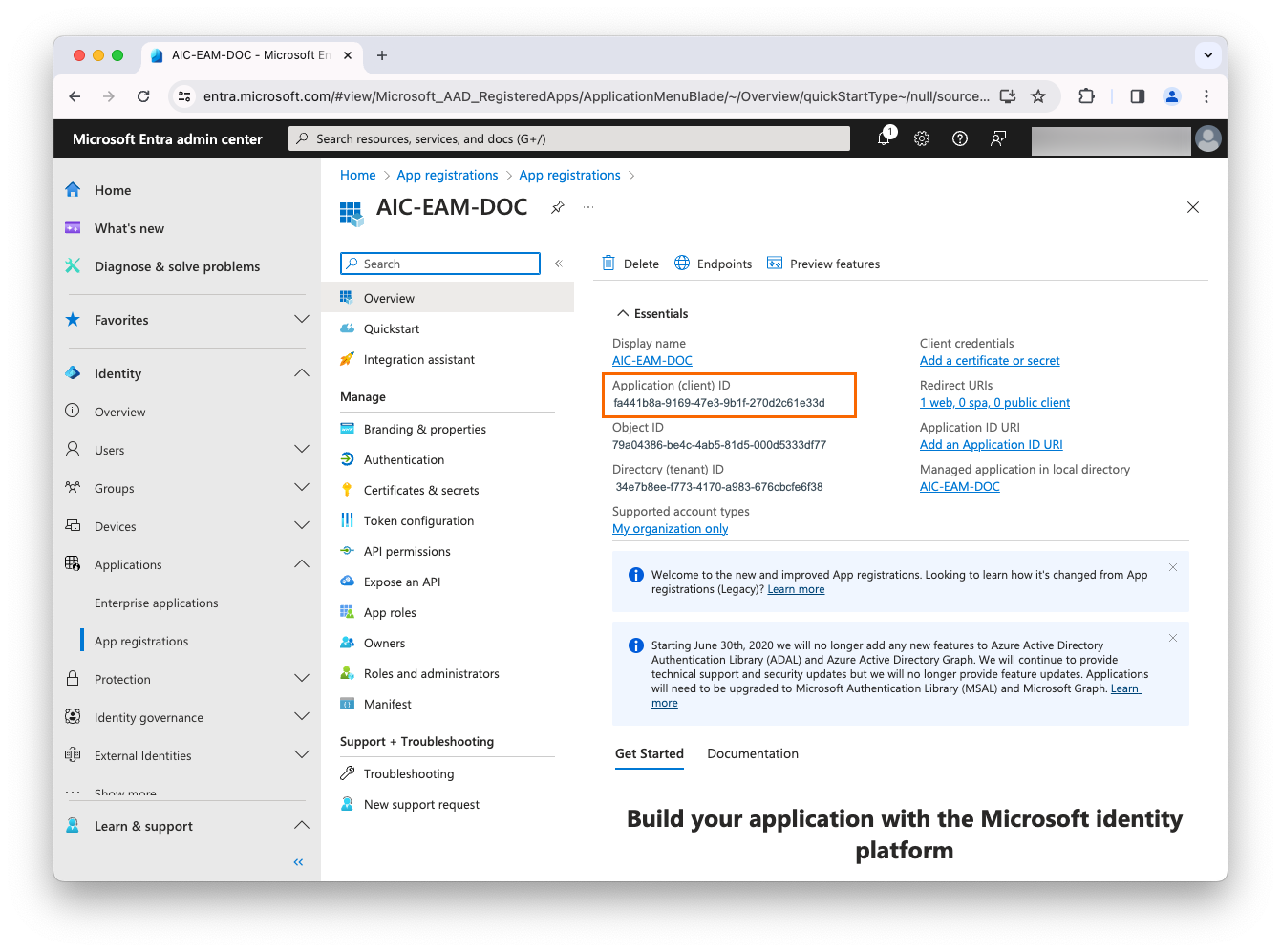
Find the application ID:
-
In the application menu, click Overview.
-
Note the Application (client) ID of the application. For example,
fa441b8a-9169-47e3-9b1f-270d2c61e33d. You’ll need this to create an external authentication method.
-
-
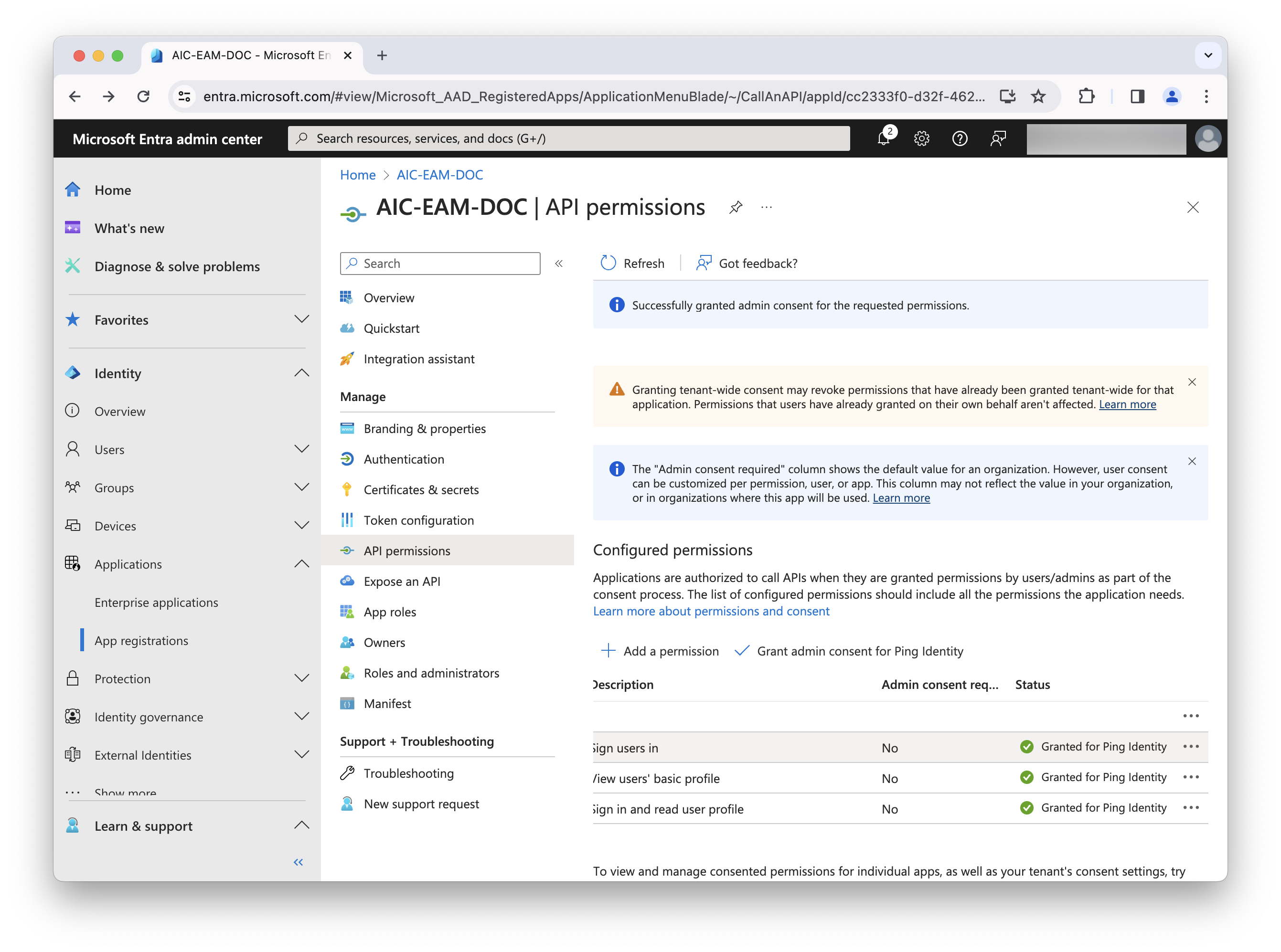
Configure the application’s permissions to the API:
-
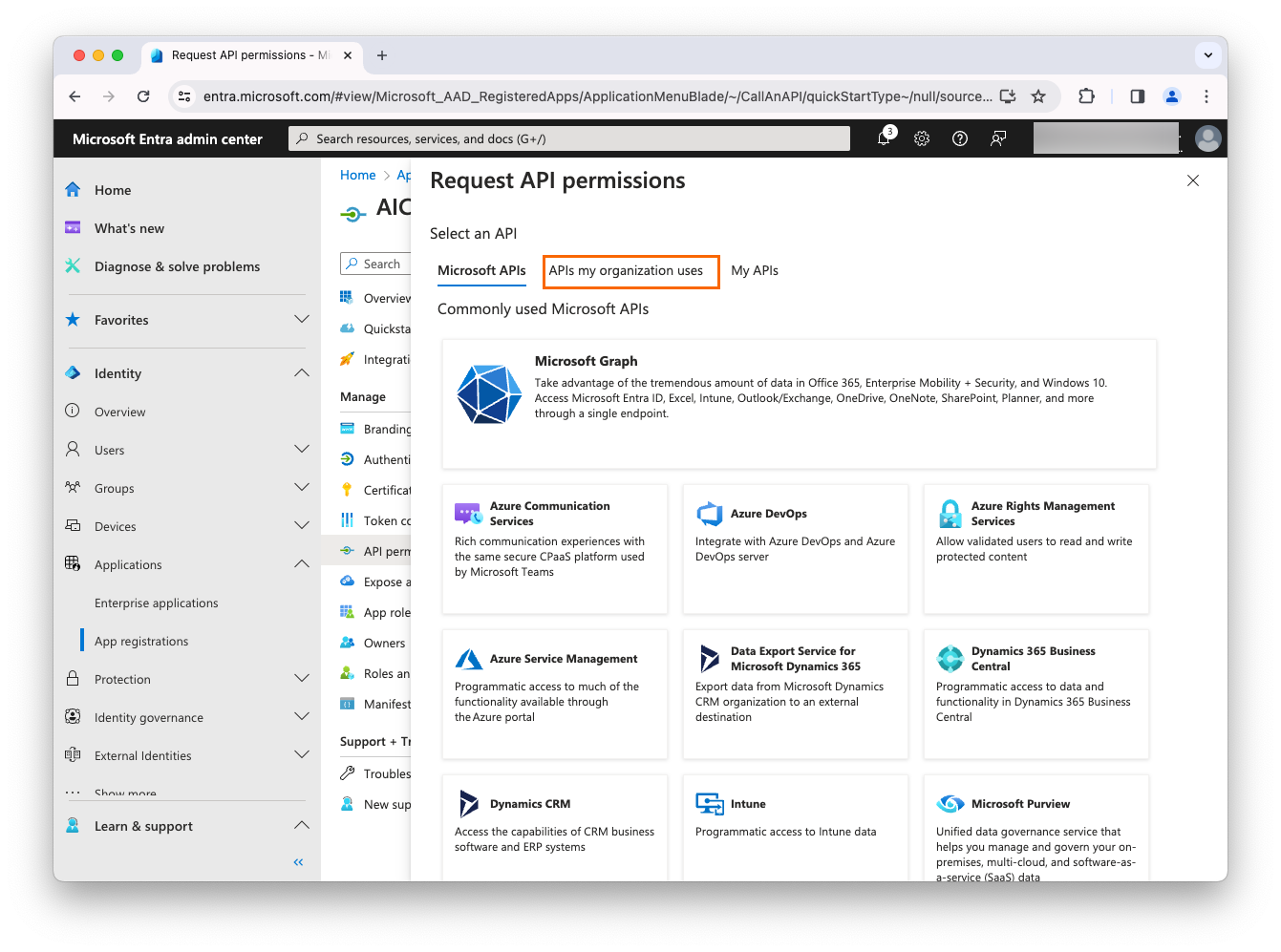
Select API permissions and then click Add a permission.
-
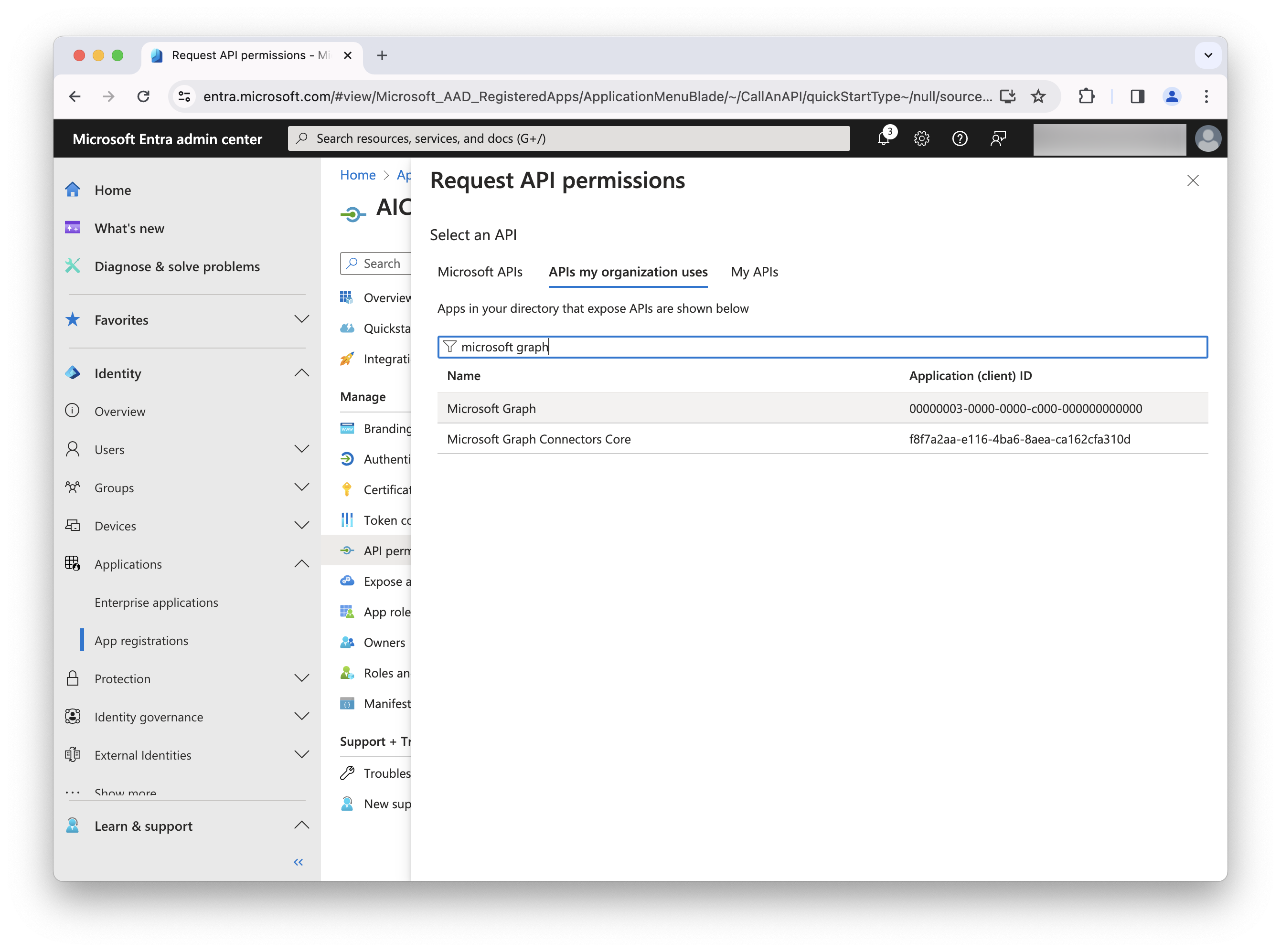
In the top toolbar, select APIs my organization uses.
-
Search for and select Microsoft Graph.
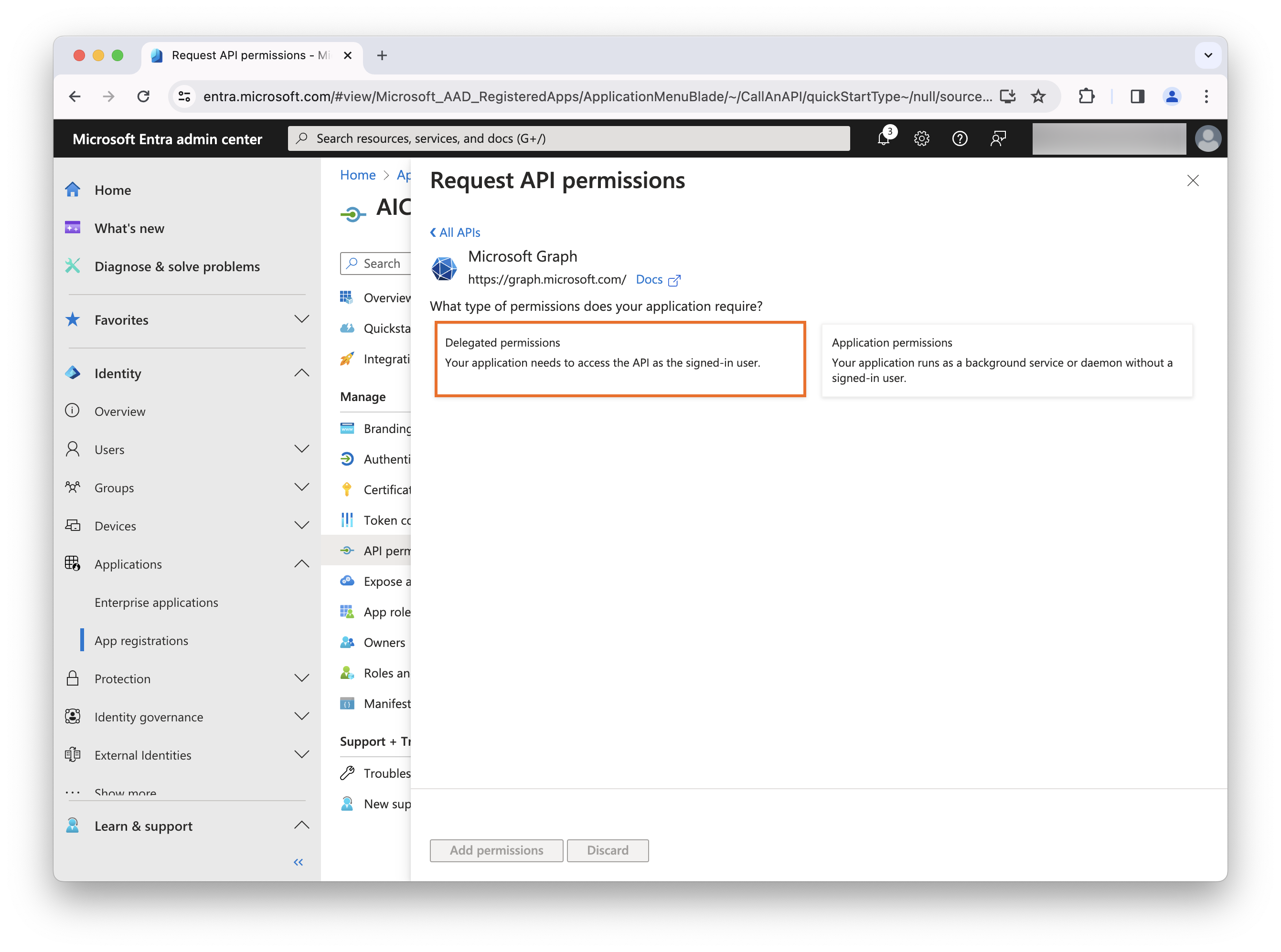
-
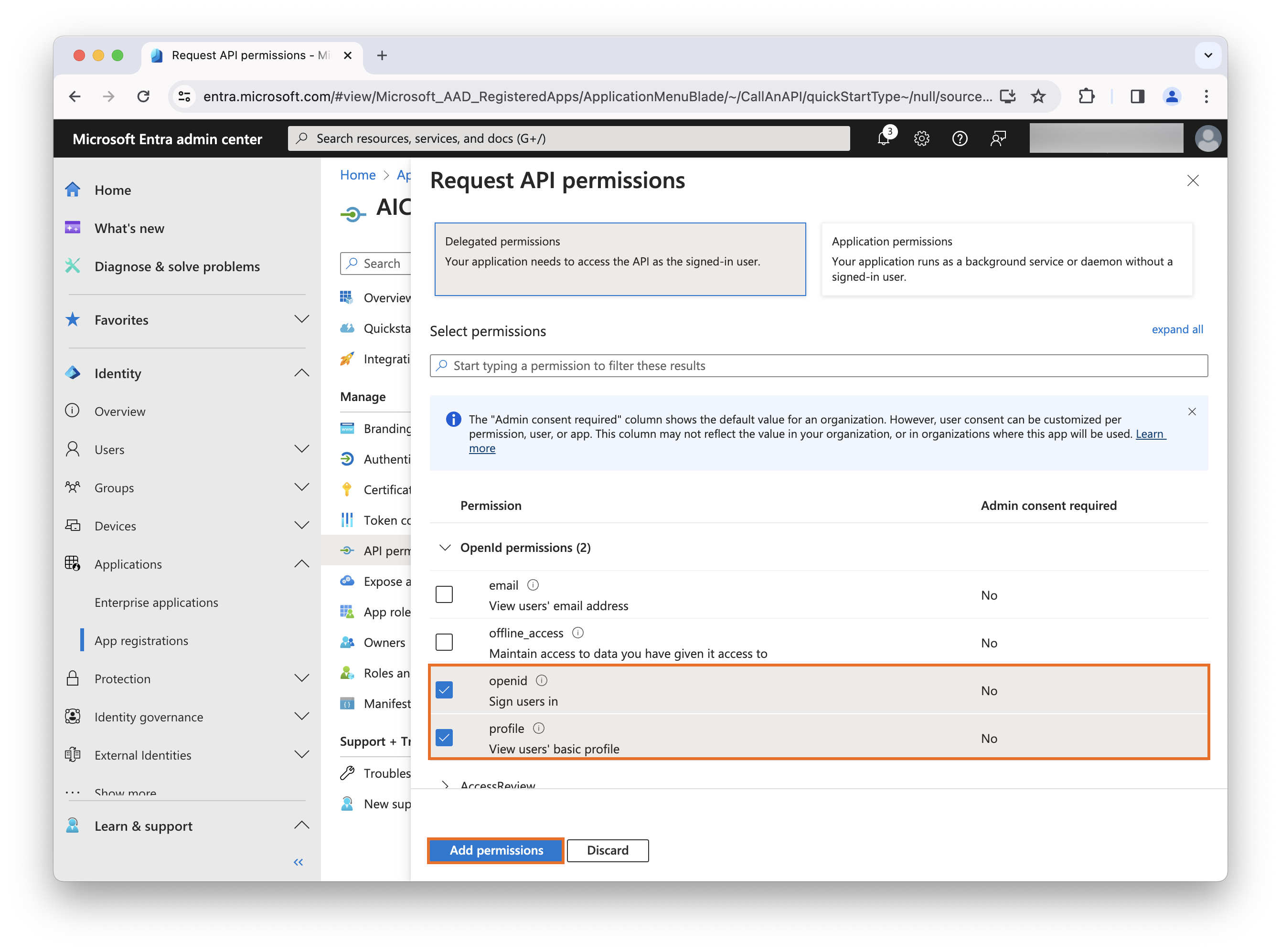
Select Delegated permissions.
-
In the Openid permissions section, select the openid and profile checkboxes, and click Add permissions.
-
Click Grant admin consent for <your company>.
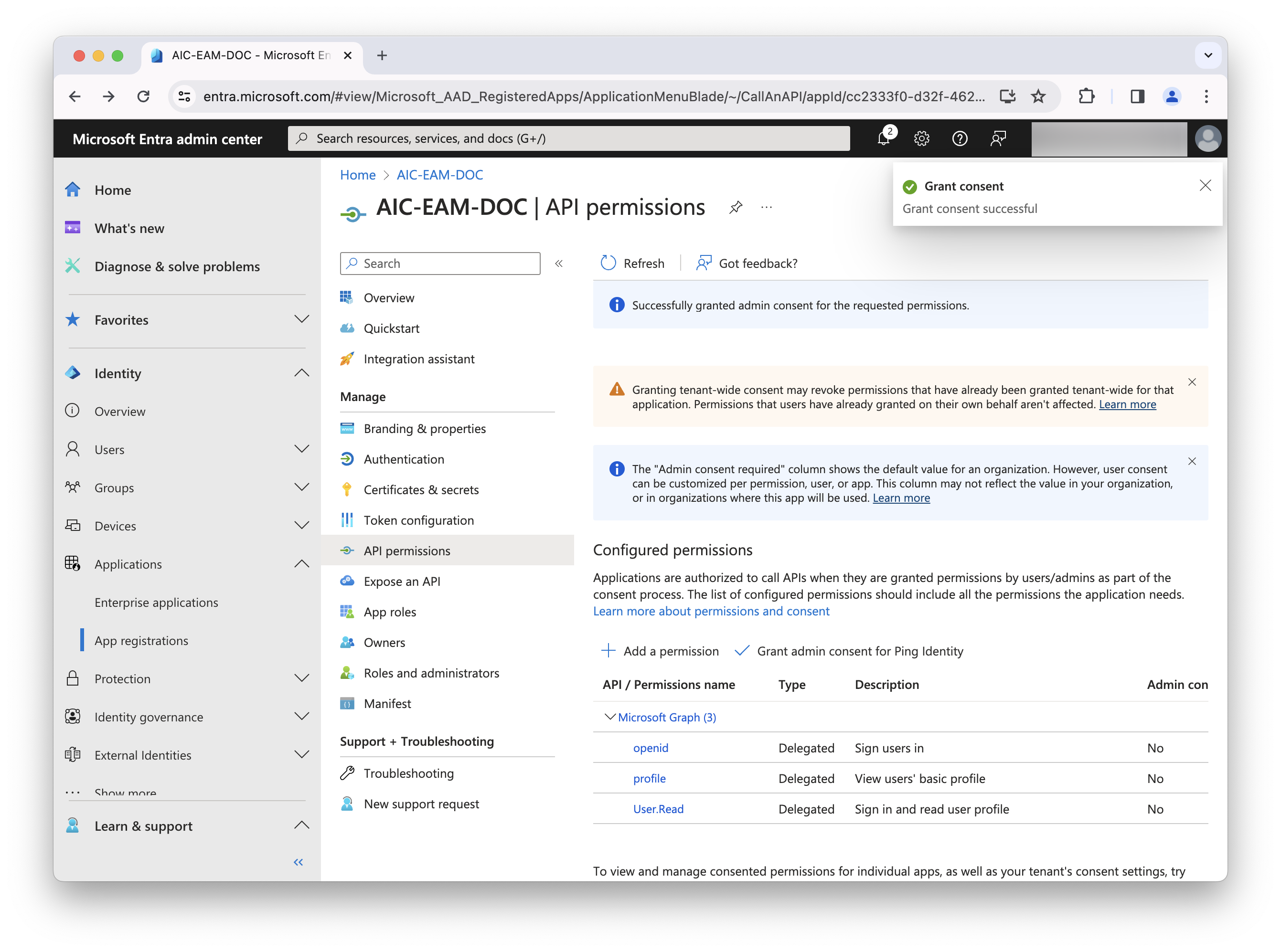
-
Complete the necessary steps for this task, including granting admin consent, and refresh the screen to display the updated permission status. Learn more in Grant tenant-wide admin consent to an application in the Microsoft Entra ID documentation.
-
Create a new group
Creating a group helps prevent all users from being locked out of the tenant when external authentication is enabled.
-
In a browser, navigate to the Microsoft Entra admin center.
-
In the left panel, click Identity and then click Groups > All groups.
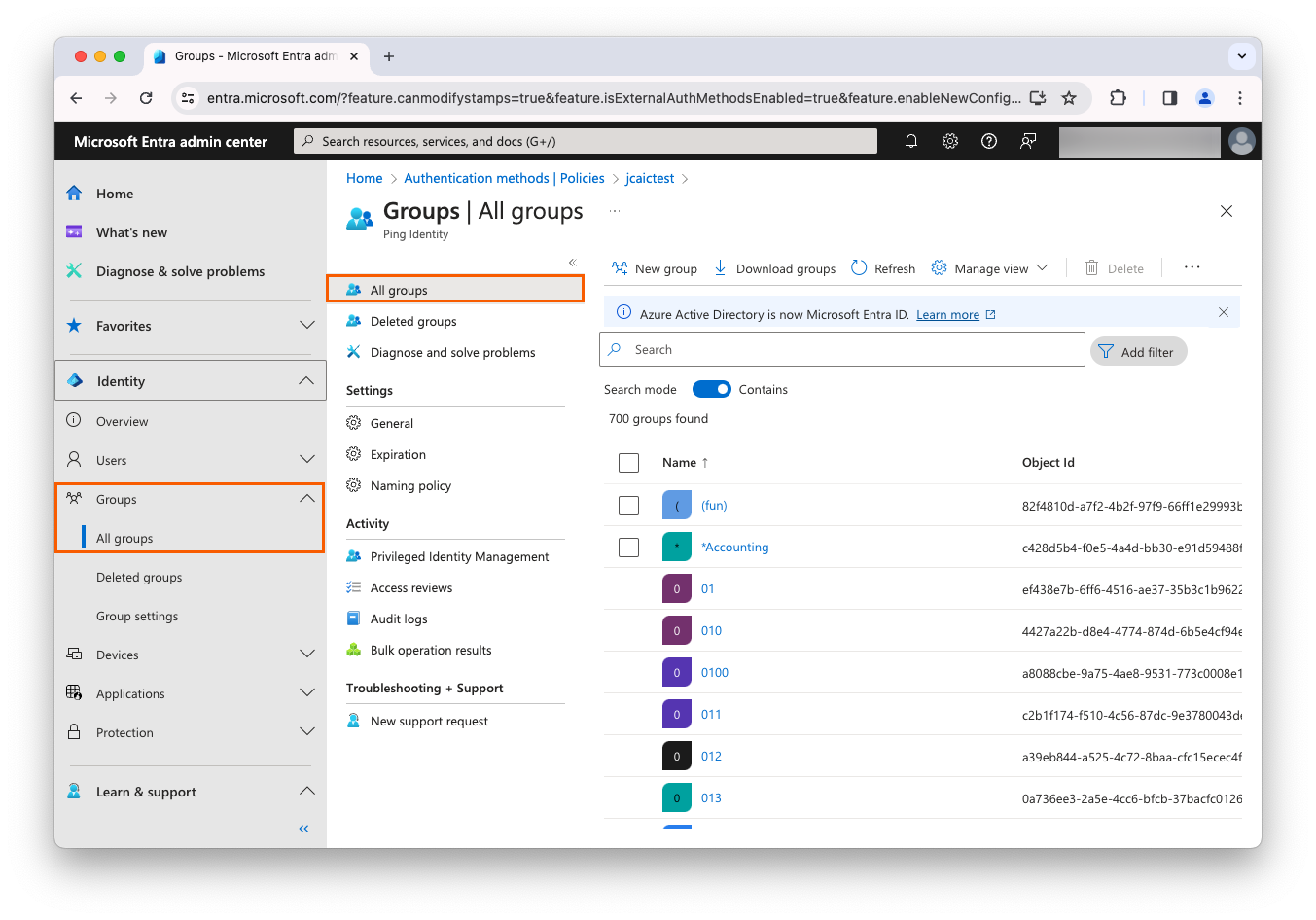
-
Click New group, and complete the following fields:
Field Value Group type
SecurityGroup Name
Anything you want
Membership type
Assigned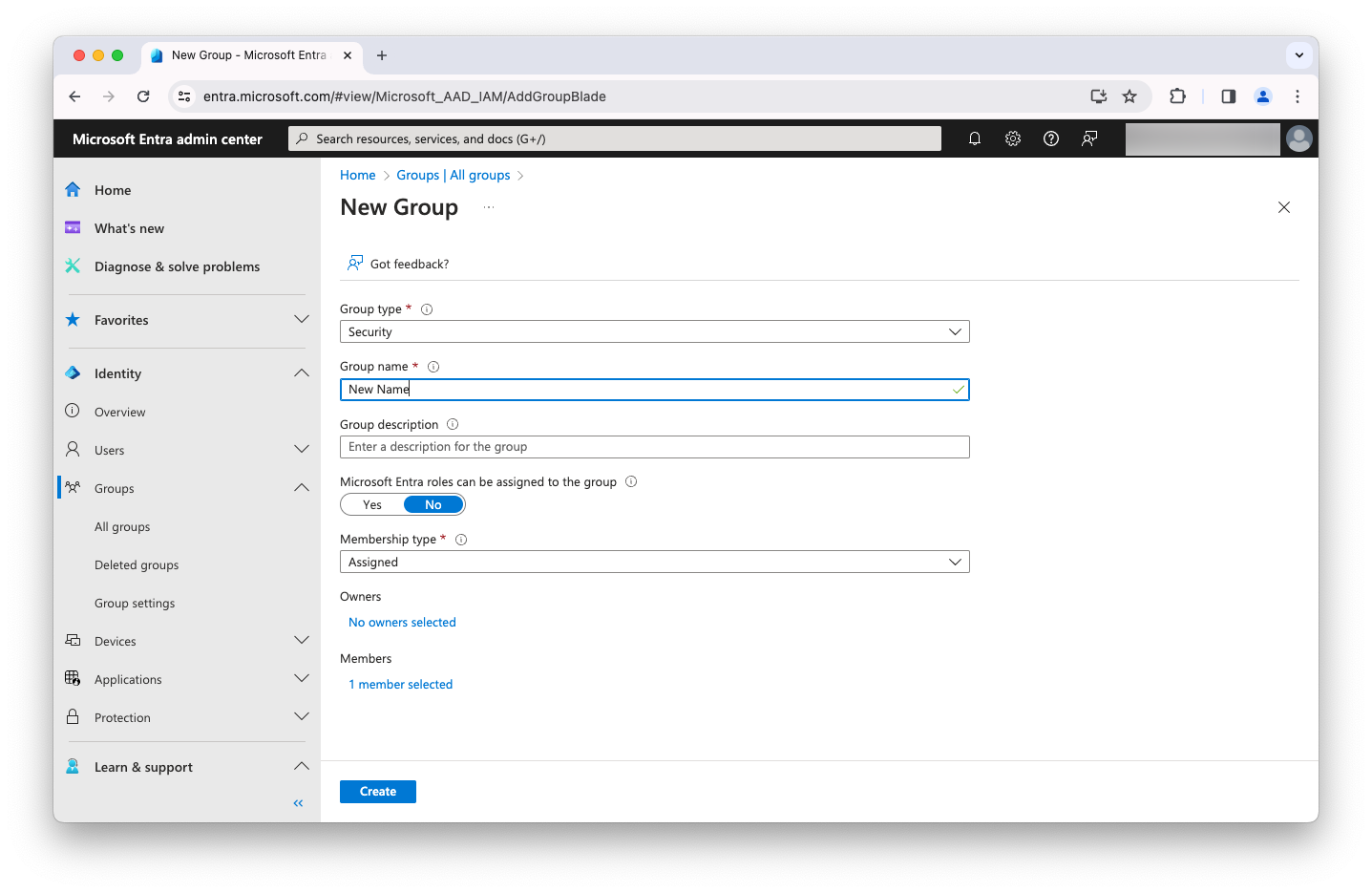
-
Add a few test users to the group, as needed.
-
Click Create.
Add a new authentication method
-
In a browser, navigate to the Microsoft Entra admin center.
-
Click Protection and then click Authentication methods.
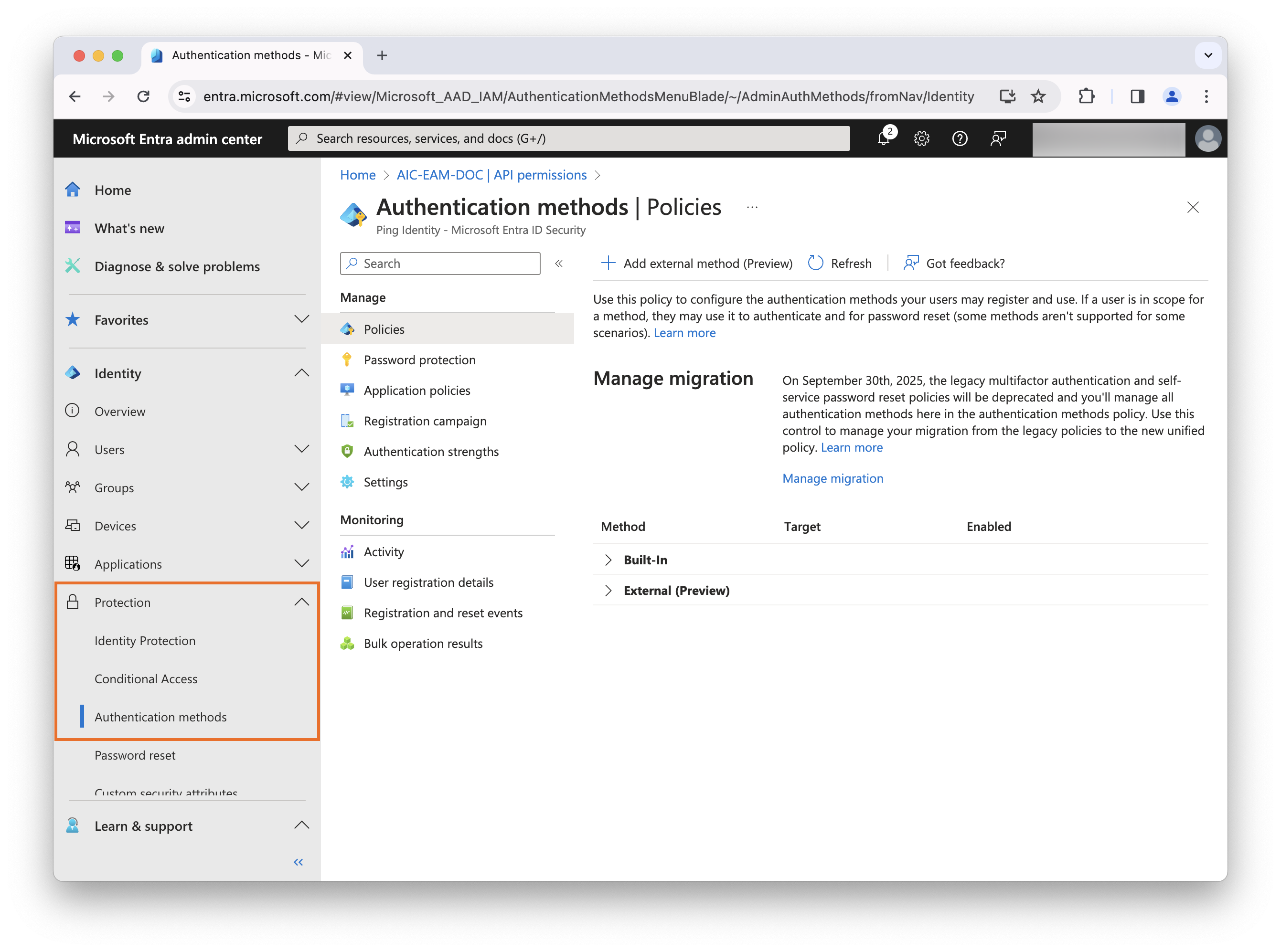
-
In the top toolbar, click Add external method (Preview). Note that this option is available only with a Microsoft Entra P1 license or higher.
-
Complete the following fields and click Save:
Field Value Name
Anything you want
Client ID
The name of the OIDC web application you created in Task 1 - Create a new OIDC web application in Advanced Identity Cloud
Discovery Endpoint
https://<tenant-env-fqdn>/am/oauth2/alpha/.well-known/openid-configurationApp ID
The generated Application (client) ID you recorded when setting up Microsoft Entra ID as the service provider
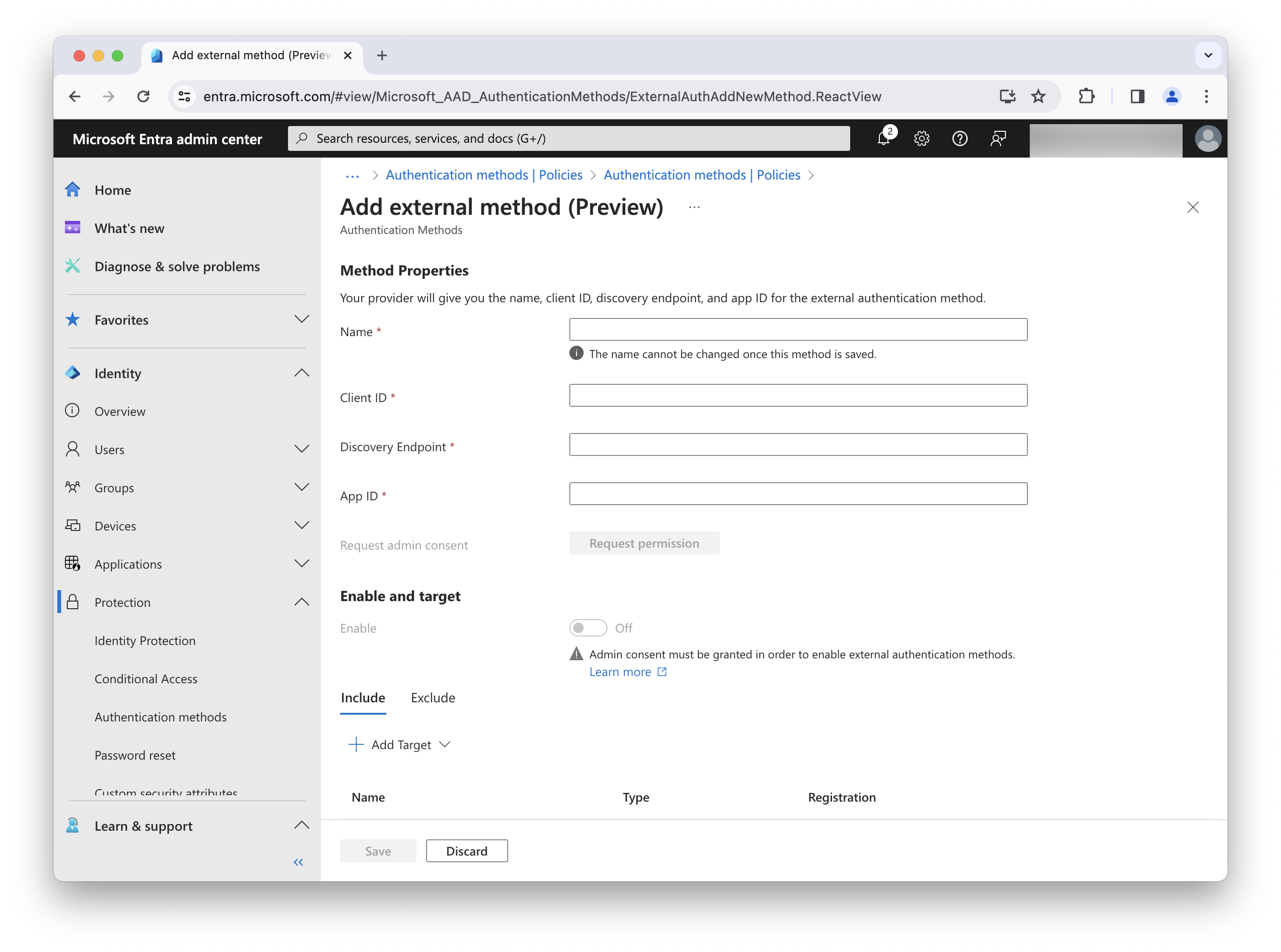
-
Ensure that you granted admin consent when you registered the new app. You need the Privileged Role Administrator or Global Administrator role to grant admin consent for the provider’s application.
-
Click the Enable toggle to enable external authentication methods.
-
Set Include or Exclude users/groups, as needed.
-
Click Save.
Create new conditional access
-
In a browser, navigate to the Microsoft Entra admin center.
-
Click Protection and then click Conditional Access.
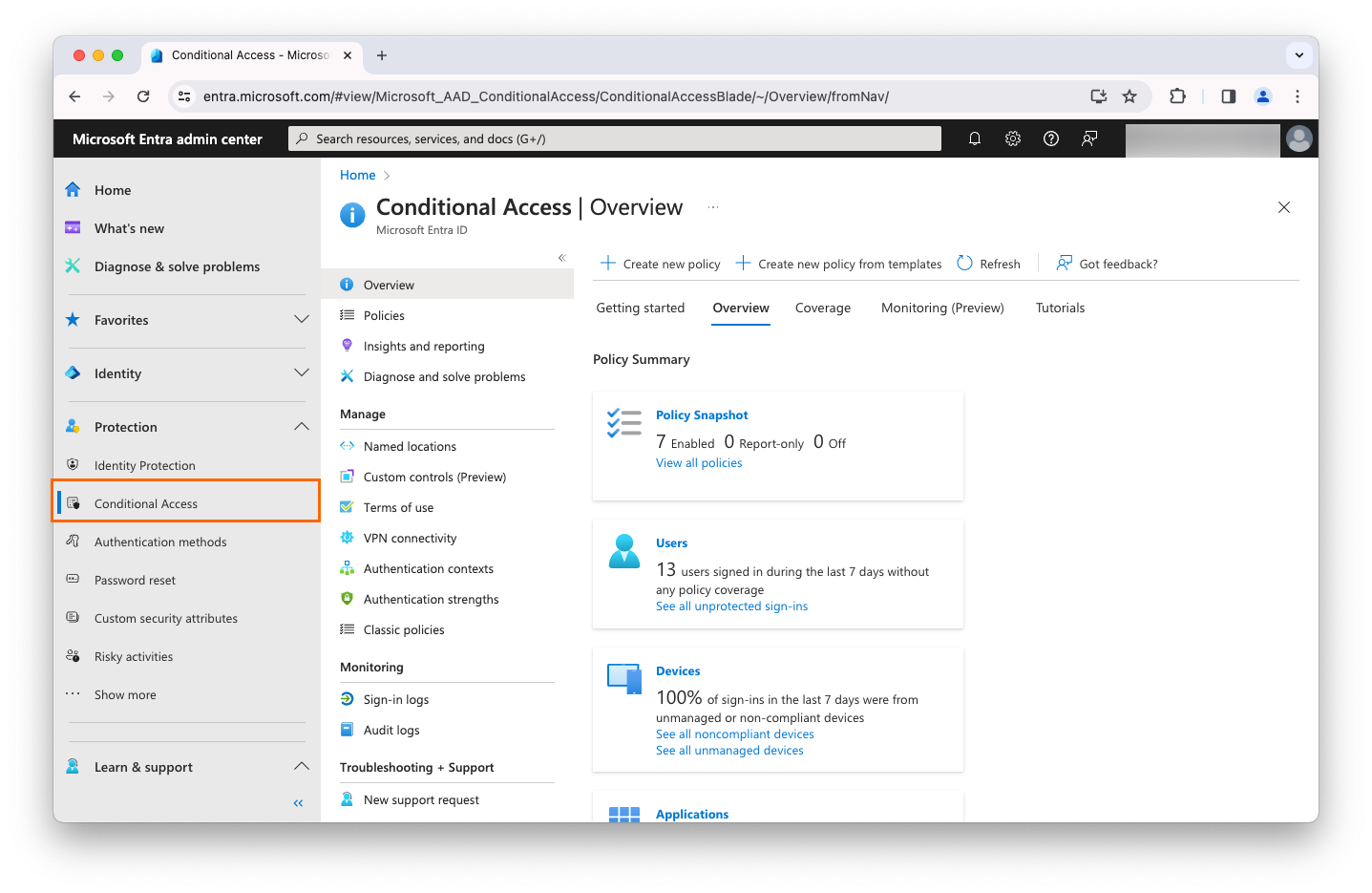
-
In the top toolbar, click Create new policy.
-
Complete the following fields:
Field Value Name
Anything you want
Users
You can add anyone you want, but you shouldn’t include all users initially in case you encounter issues. Instead, use the group you created.
Target resources
Apps you want to protect (My Apps for testing purposes)
Network
Set as needed
Condition
Set as needed
Grant
Grant access selected: Select Require multifactor authentication
Grant
For multiple controls: Set according to your security model
-
Confirm your settings and set Enable policy to Report-only.
-
Click Create.
Task 3: Complete set up of Microsoft Entra ID in Advanced Identity Cloud
|
Learn more in Override the audience and issuer claims. |
-
In the Advanced Identity Cloud admin console, go to Scripts > Auth Scripts.
-
Make a copy of the
Alpha OIDC Claims Script, and add the following lines in thegetComputedClaimsfunction, right beforereturn computedClaims;:} }); //MS Entra EAM var recievedSub = session.getProperty("eamsub"); computedClaims.put("sub", recievedSub); var amrMFAUsed = session.getProperty("eam-mfa-type"); var amrClaim = [amrMFAUsed]; computedClaims.put("amr", amrClaim); return computedClaims; } -
Update your OIDC client:
-
Go to Native Consoles > Access Management > Applications > OAuth 2.0 > Clients and click the client you created in Task 1 - Create a new OIDC web application in Advanced Identity Cloud.
-
On the Core tab, complete the following fields:
Field Value Redirection URIs
https:// login.microsoftonline.com/common/federation/externalauthproviderDefault Scope(s)
openidprofile -
On the Advanced tab, complete the following fields:
Field Value JavaScript Origins
https://login.microsoftonline.com
https://login.microsoftonline.com:443Response Types
id_tokenGrant Types
ImplicitToken Endpoint Authentication Method
None -
On the OAuth2 Provider Overrides tab, complete the following fields:
Field Value Enable OAuth2 Provider Overrides
Enabled
Access Token Modification Plugin Type
ScriptedAccess Token Modification Script
Alpha OAuth2 Access Token Modification ScriptOIDC Claims Plugin Type
SCRIPTEDOIDC Claims Script
Name of the script you created in step 2
OIDC Claims Plugin Implementation Class
org.forgerock.openam.oauth2.OpenAMScopeValidatorUse Client-Side Access & Refresh Tokens
Enabled
Allow Clients to Skip Consent
Enabled
Scope Evaluation Plugin Implementation Class
org.forgerock.openam.oauth2.OpenAMScopeValidatorScope Validation Plugin Type
JAVAScope Validation Plugin Implementation Class
org.forgerock.openam.oauth2.OpenAMScopeValidatorAuthorize Endpoint Data Provider Plugin Type
SCRIPTEDAuthorize Endpoint Data Provider Script
OAuth2 Authorize Endpoint Data Provider ScriptAuthorize Endpoint Data Provider Plugin Implementation Class
org.forgerock.openam.oauth2.OpenAMScopeValidatorOverrideable Id_Token Claims
subacramr -
Click Save Changes.
-
-
Whitelist the EAM session properties:
-
Go to Services > Session Property Whitelist Service.
If the Session Property Whitelist Service is not listed, click Add a Service to add it. -
In the Allowlisted Session Property Names and Session Properties to return for session queries fields, enter
eamsubandeam-mfa-type, and click Save Changes.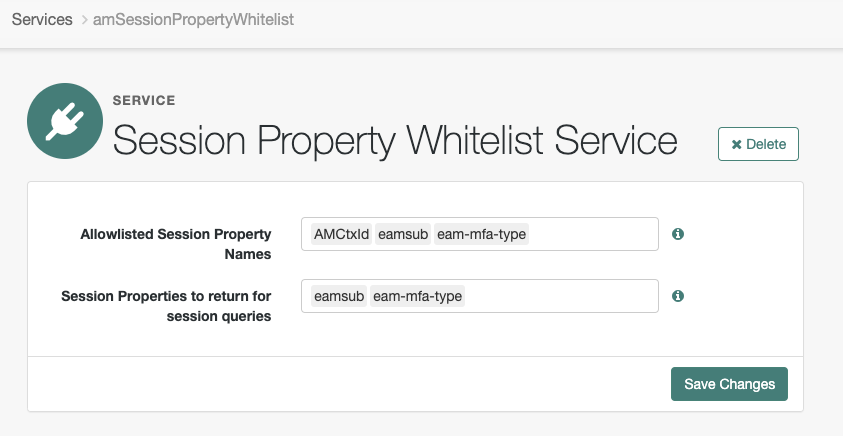
-
-
Import and configure the sample journey:
-
In the Advanced Identity Cloud admin console, import this sample journey. Learn more about importing journeys in Import journeys.
This journey is provided as an example only. It isn’t configured to perform multi-factor authentication (MFA).
The scripts provided with the journey are samples and are not supported by Ping Identity.
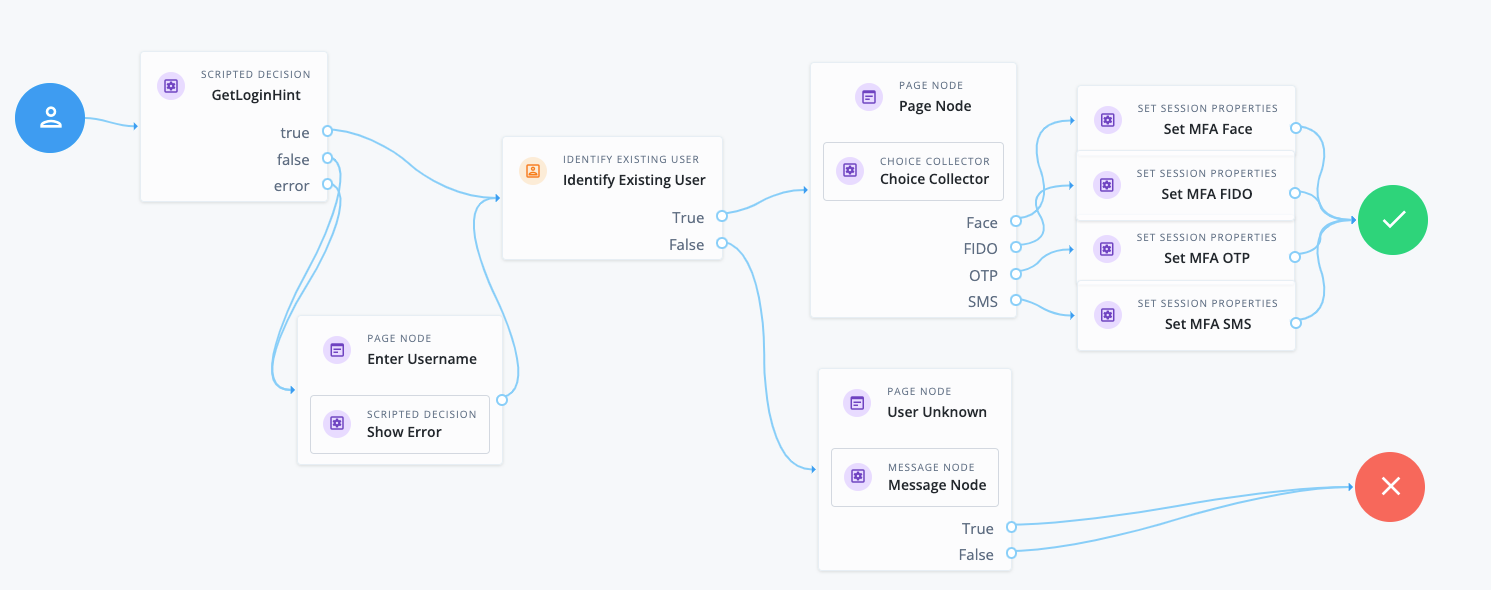
-
In the GetLoginHint node, open the
EAMGetLoginHintscript and update the configuration variables with your EAM-specific data. This script takes the redirect from Microsoft Entra ID with a signed JWT containing the username to authenticate the user within the journey.Field Value issuer
The issuer URL in the format
https://login.microsoftonline.com/<tid>/v2.0.To find your EAM tenant ID (tid), go to the Microsoft Entra admin center and click Identity > Overview. jwksJson
The full JWKS that can be found at
https://login.microsoftonline.com/<tid>/discovery/v2.0/keysaudience
The generated Application (client) ID you recorded when setting up Microsoft Entra ID as the service provider.
tid
Your EAM tenant ID (tid)
nodeName
The node name, which is used for logging purposes.
-
-
Go to Native Consoles > Access Management > Services > OAuth2 Provider.
-
On the Advanced OpenID Connect tab, update your OAuth 2.0 Provider by completing the following fields:
Field Value Enable "claims_parameter_supported"
True (on)
OpenID Connect acr_values to Auth Chain Mapping
possessionorinherence: EAM SAMPLE (the sample journey name)
Validation
Now that you have created and configured the EAM setup, validate the configurations.
Steps
-
In a browser, go to https://myapps.microsoft.com.
-
Sign in using the test user’s username and password.
-
When prompted, select the external authentication method you configured.
-
Choose your MFA method (this assumes the journey administrator has configured an MFA challenge).
Upon successful authentication, the user should be logged into Microsoft Entra ID.